Overview of Kubernetes v1.35 Release
The launch of Kubernetes v1.35 marks another milestone in the continuous evolution of this open-source project. Mirroring past releases, it brings an impressive collection of enhancements, totaling 60 new features that break down into 17 stable updates, 19 in beta, and 22 still at the alpha stage. This broad spectrum of improvements illustrates not only the active participation of the Kubernetes community but also the project's commitment to consistently delivering high-quality updates.
With ongoing development fueled by a diverse global network of contributors, the latest version showcases the platform’s robustness. However, along with these updates, there are also some deprecations and removals worth reviewing to ensure that users are aware of any potential impacts on existing setups.
Theme and Visual Identity of the Release
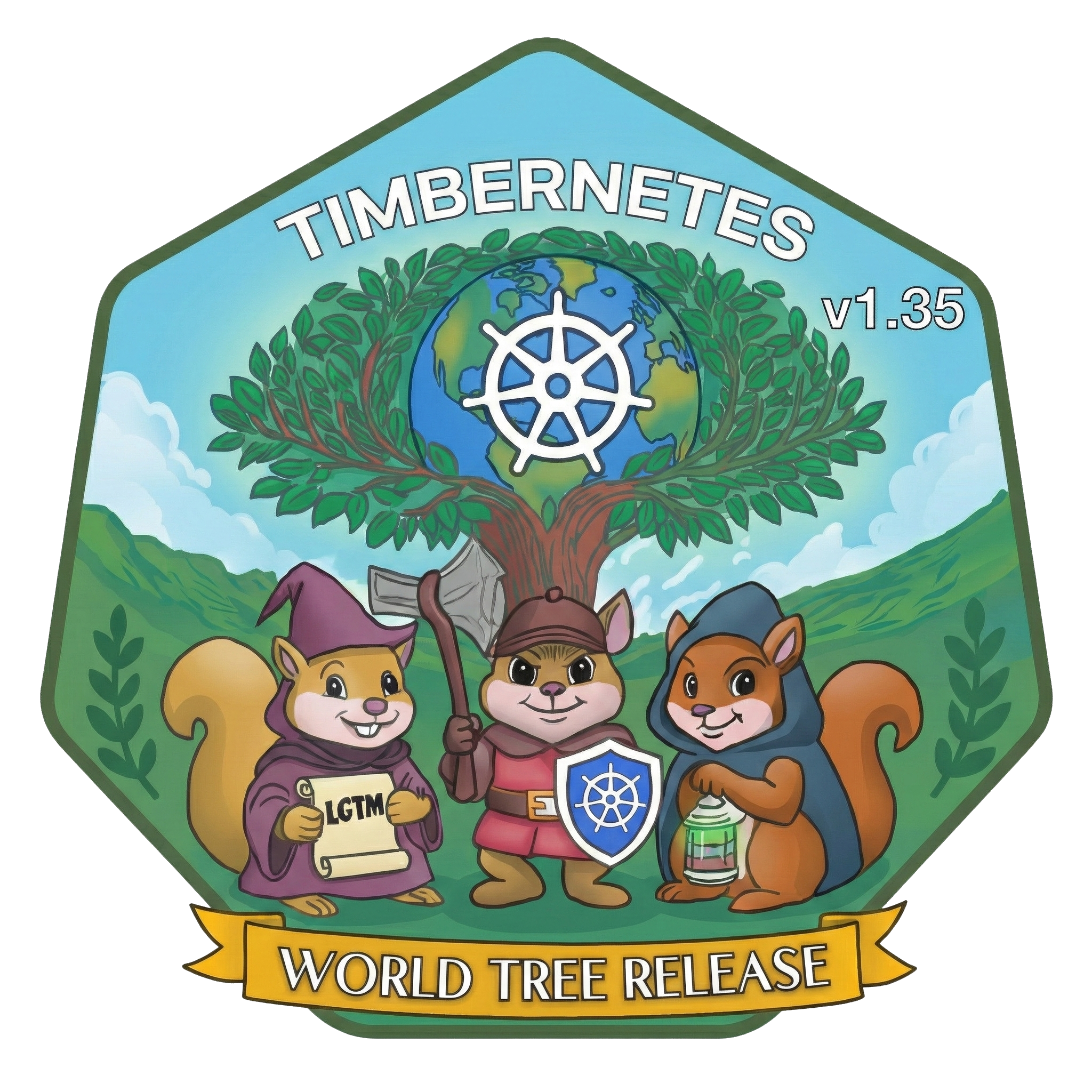
Each Kubernetes release features a thematic element to reinforce its identity, and v1.35 is no exception, drawing inspiration from Yggdrasil, the mythical tree that connects different realms. This year's theme is aptly dubbed the "World Tree," symbolizing how Kubernetes matures incrementally—with each release adding another ring to its trunk. The logo encapsulates this narrative beautifully, featuring a vivid world tree and characters that embody the community's spirit.
The design includes three squirrels, each representing different roles within the ecosystem: a wizard responsible for code reviews with an LGTM scroll, a warrior equipped to handle the cutting-edge features, and a rogue illuminating the complexities of issue triaging. This whimsical reflection on teamwork accentuates the collaborative nature that keeps Kubernetes thriving.
If you’re engaged in Kubernetes development, this ongoing growth narrative underlines the platform's longevity and resilience, as its community continues to nurture and refine it.
Enhancements to Horizontal Pod Autoscaling
For far too long, the Horizontal Pod Autoscaler (HPA) operated under the constraint of a rigid 10% tolerance for scaling. This limitation meant that workloads needing rapid adjustments based on smaller changes—like a 5% load spike—often couldn’t scale as necessary. On the flip side, certain applications would trigger unnecessary scaling actions, leading to inefficiencies. Now, with the advent of Kubernetes v1.35, users can breathe a sigh of relief. This version rolls out beta support for configurable tolerance, activated by default, allowing operators to specify tolerance levels for scaling on a per-resource basis through the HPA's `behavior` field. For instance, if you drop the tolerance to 0.05 for a 5% increase, your critical applications can scale responsively to minor fluctuations without needing complex cluster-wide changes.
This significant shift in autoscaling dynamics is a product of KEP #4951, driven by SIG Autoscaling. It’s more than just a nice feature; it empowers DevOps teams to fine-tune their resource management, leading to potentially better performance and cost management. If you're in this field, adopting this new capability could give you the edge in handling sensitive workloads.
User Namespace Support in Pods
Kubernetes is stepping up its security game by adding support for user namespaces, which is a critical enhancement for pod security. This improvement allows containers to utilize isolated user and group ID mappings rather than relying on the shared host IDs. This means that a pod can operate as root internally while mapping to a non-privileged user outside, which significantly reduces the risk of privilege escalation if any container were compromised. This feature enhances security at the pod level, particularly for workloads requiring root permissions, and extends support to both stateless and stateful Pods with id-mapped mounts. The work around this was outlined in KEP #127, led by SIG Node. If you're involved in managing workloads, the implications of this update cannot be overstated; it creates a safer environment for running applications that require escalated privileges, thus improving overall cluster security.Integration of Volume Source for OCI Artifacts
When deploying Pods, the need to provide essential configuration files, binaries, or data usually meant embedding them within the main container image or utilizing an init container, which could complicate the process. Kubernetes v1.31 introduced a significant change by adding support for the `image` volume type. This allows Pods to directly pull and unpack OCI container image artifacts as needed.
This new approach facilitates a cleaner separation of your data from the container image itself, eliminating the necessity for additional init containers or complex scripts. The image volume type has been in beta since version v1.33 and becomes a default feature in v1.35. However, do note that users will need a compatible container runtime, such as containerd v2.1 or later, to take advantage of this functionality. Thanks to KEP #4639, crafted by SIG Node, this feature streamlines deployment processes, particularly beneficial for teams aiming for efficiency in development workflows.
Enhanced Security with Kubelet Credential Verification
The security model around cached images in multi-tenant clusters has received a crucial overhaul. Previously, under the `imagePullPolicy: IfNotPresent` setting, a Pod could utilize cached images on a node without confirming whether it possessed the right credentials to access those images. This loophole could open doors to unauthorized access, especially in environments where sensitive images are stored. In Kubernetes v1.35, a new feature introduces credential verification for cached images, requiring the `kubelet` to validate that a Pod has the appropriate credentials before it can use a locally cached image. This ensures that even cached images remain under strict access control, reinforcing security across shared clusters. It’s enabled by default in v1.35, though operators retain the option to customize this with the `KubeletEnsureSecretPulledImages` feature gate.
This work stems from KEP #2535, led by SIG Node, and its impact on security policy for multi-tenant clusters is substantial. If you're managing sensitive workloads, this should definitely be on your radar as it significantly tightens your cluster's security posture.

